FTC disclaimer: This post contains affiliate links and I will be compensated if you make a purchase after clicking on my link.
You would have heard of “network protocol” or simply “protocol” so many times. Sometimes, the protocol is being used in reference to works and standards without explaining them.
Other than networking protocols, you would have also heard of internetworking protocols, high-level protocols, low-level protocols, protocol suites, protocol stacks, sub-protocol, and so on.
These protocol terms may be vague and can have so many meanings, difficult to understand and grasp.
What is the protocol? A Human Analogy
In the real world, the protocol refers to a set of rules, code of conduct, the official procedure, a form of etiquette, or a system of rules governing state affairs.
So, as per the understanding of the above meaning, one can conclude that protocols refer to a certain set of rules which make your communication efficient and effective without any conflict.
You would have observed that when there is an interaction between two representatives of two different nations, then it is expected that each representative should be familiar with their local customs.
This way, normal people follow various protocols, and some sorts of protocols are “unwritten rules of society.”
A human analogy
Considering human analogy help, you understand better how computer network protocol works.
Let’s consider a human analogy. Suppose you sit in a class and listen to a lecture ( a computer networking class, for example).
The teacher explaining some concepts of networking, but you are confused. After completing some topic, the teacher asks, “Are there any questions?” ( A message is transmitted and received by all the students listening to this lecture).
You raise your hand and ask permission (transmitting an implicit message and waiting for permission from the other end).
Your teacher acknowledges you and gives permission to share your doubt (the transmitted message was acknowledged and agree for further communication).
You have asked your question (the message was transmitted). Your teacher received your question (the message was received to the other end).
Your teacher replied to your question (reply message was transmitted). Next, you have accepted the reply (transmitted reply message was accepted).
Thus, how the transmission and receipt of message take place in this question-and-answer protocol. Also, the action taken when these messages are sent, received, or other events occur.
What are Network Protocols?
A network protocol is very similar to a human protocol.
In-network protocol, entities involved in exchanging messages and taking actions are hardware and software components of a computer network.
All activity on the internet involves two or more communicating entities, which is governed by protocols.
A network protocol ensures that all the devices in a network or internetwork agree about how the actions must be performed in a complete communication process.
Additionally, the individual protocol also describes how the communication process should be accomplished between one particular hardware or software element in two or more devices.
Definition of network protocol
A networking protocol defines a set of rules, algorithms, and other mechanisms for formatting and processing data that enables software and hardware elements in a networking device to communicate with each other effectively.
In the OSI reference model context, a network protocol defines a set of rules governing the communication between corresponding entities at the same reference model layer.
For instance, the transmission control protocol, layer four of the OSI model, is responsible for specific functions on TCP/IP networks.
So, each host in a TCP/IP network must have TCP implementation to communicate with each other effectively.
Standardized protocol in a network is just like the common language of a computer, which is approved and agreed globally to communicate effectively.
If one computer is having Internet Protocol (IP), then others should have the same to communicate with each other.
There are different types of protocol on the internet, and each protocol is responsible for different types of processes.
Protocol in a network is often related and discussed in terms of layers of the OSI reference model.
How Network Protocols work?
Network protocols break down the large-scale process into small, specific tasks or functions.
This process occurs in every layer of the network, and each function or task must cooperate with the other to complete the larger tasks or functions.
The term protocol suite, such as TCP/IP protocol suite, refers to all smaller protocols or sets of protocols that work in conjunction with each other in the different network layer.
Network protocols are typically created, defined, and published according to the industry standard by various networking or information technology organization.
The following groups are responsible for creating and publishing network protocols:
- The Institute of Electrical and Electronics Engineers (IEEE)
- The Internet Engineering Task Force (IETF)
- The International Organization for Standardization (ISO)
- The International Telecommunications Union (ITU)
- The World Wide Web Consortium (W3C)
Each protocol which is developed and created by these group are unique and operates in a specific way.
Who uses network protocols?
The network protocol is not only relevant to network professionals, but it is used by billions of people daily, whether they know it or not.
Every time you use the internet or do some digital communication, you are using network protocols. Though you may don’t know how network protocol works and how frequently you are using it.
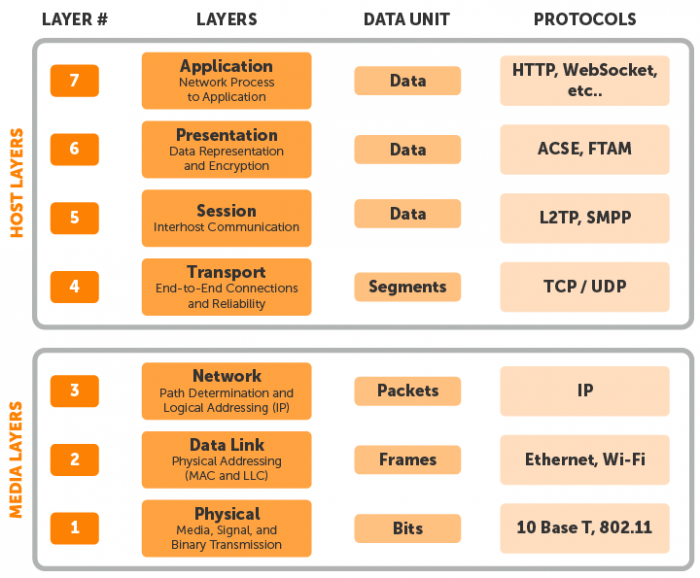
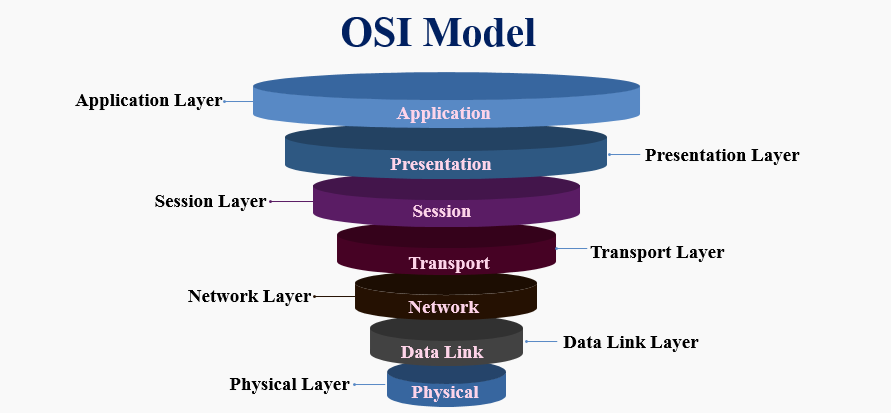
What are the different layers of the OSI model?
The Open Systems Interconnection (OSI) model is an abstract and conceptual representation of how the internet works.
It consists of 7 layers, and each layer is responsible for performing different network functions.
Application layer (Layer 7): It is an interaction layer where the application access the network services and communicates with other computers in a network.
Presentation layer (Layer 6): This layer’s main function is defining and ensuring data formation and encryption.
Session layer (Layer 5): It is responsible for maintaining the connection and controlling the sessions and ports.
Transport layer (Layer 4): It is responsible for delivering data to the appropriate application process on the host computers.
Network layer (Layer 3): This layer decides the actual physical path the data should take.
Datalink layer (Layer 2): This layer decides how the stream bits are put together into manageable chunks of data.
Physical layer (Layer 1): This layer’s function describes how the data (raw bitstream) is transmitted over a network medium.
Most common network protocol
Internet Protocol (IP): It is a network layer protocol that makes network-to-network communication possible. It is responsible for routing data packets from source to destination.
The transmission control protocol (TCP): It is a transport layer protocol that ensures that the transportation of data packets across the network goes smoothly.
User Datagram Protocol (UDP): The User Datagram Protocol is in the Transport Layer and alternative to Transmission Control Protocol (TCP). It is fast but less reliable compare to Transmission Control Protocol.
Internet Control Message Protocol (ICMP): The Internet Control Message Protocol reports an error and provides delivery status updates.
Hypertext Transfer Protocol (HTTP): It belongs to the Application Layer (Layer 7) and helps transfer data between devices. It converts the data into a format that makes it available to an application-like browser for further interpretation.