FTC disclaimer: This post contains affiliate links and I will be compensated if you make a purchase after clicking on my link.
We live in a world where our personal information is constantly stolen. We’ve seen it repeatedly happen, from credit card numbers to bank account passwords. It’s not just hackers stealing data, either. Government agencies are also known to steal private information.
When you encrypt something, you ensure only someone who knows the encryption key can read it. This means that even if someone steals your password, they won’t be able to access your email or social media accounts because they don’t have the correct decryption key.
Encryption has become increasingly important as technology advances. Many companies will charge extra fees to customers who don’t encrypt their sensitive data. For example, banks often require customers to enter their PIN numbers before withdrawing.
If you’re wondering how to protect yourself online, then read on. We will explain everything you need to know about encryption and why it’s important for protecting your privacy.
Understanding Encryption
What is encryption?
Encryption is a way of protecting sensitive information. For example, you might want to encrypt a document containing personal financial information such as credit card numbers or bank account passwords. Or maybe you’re sending confidential emails about a project at work. You could even encrypt your online banking login credentials.
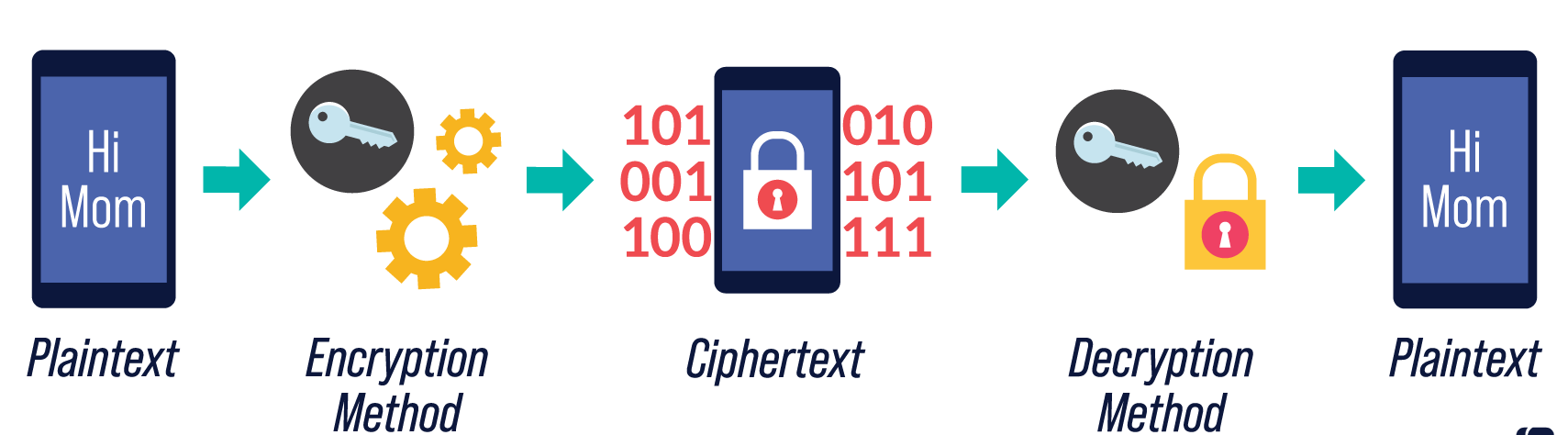
In simple terms, encryption converts human-readable plaintext into unintelligible ciphertext. This makes it impossible for anyone except the intended recipients to read the contents.
In technical terms, this involves transforming the original plaintext to produce ciphertext. The transformations make it difficult to reverse the conversion, making it almost impossible to decipher the original message without knowing the secret key used to perform the transformation.
The most common type of encryption is symmetric cryptography. Symmetric keys are generated once and shared among multiple users.
They provide confidentiality—the ability to keep messages secure during transmission—and integrity—ensuring that the message hasn’t been tampered with along the way.
There are many different types of symmetric ciphers. Some are based on block ciphers, where each piece of plaintext is broken up into blocks and encrypted separately. Others rely on stream ciphers, where the whole message is encrypted in one go.
There are also hybrid methods, like the Advanced Encryption Standard (AES), which combines elements of both block and stream ciphers.
Some encryption algorithms are public, meaning anyone can learn how to decrypt the resulting ciphertext. Other algorithms are kept secret, meaning only those with the proper access can unlock the message.
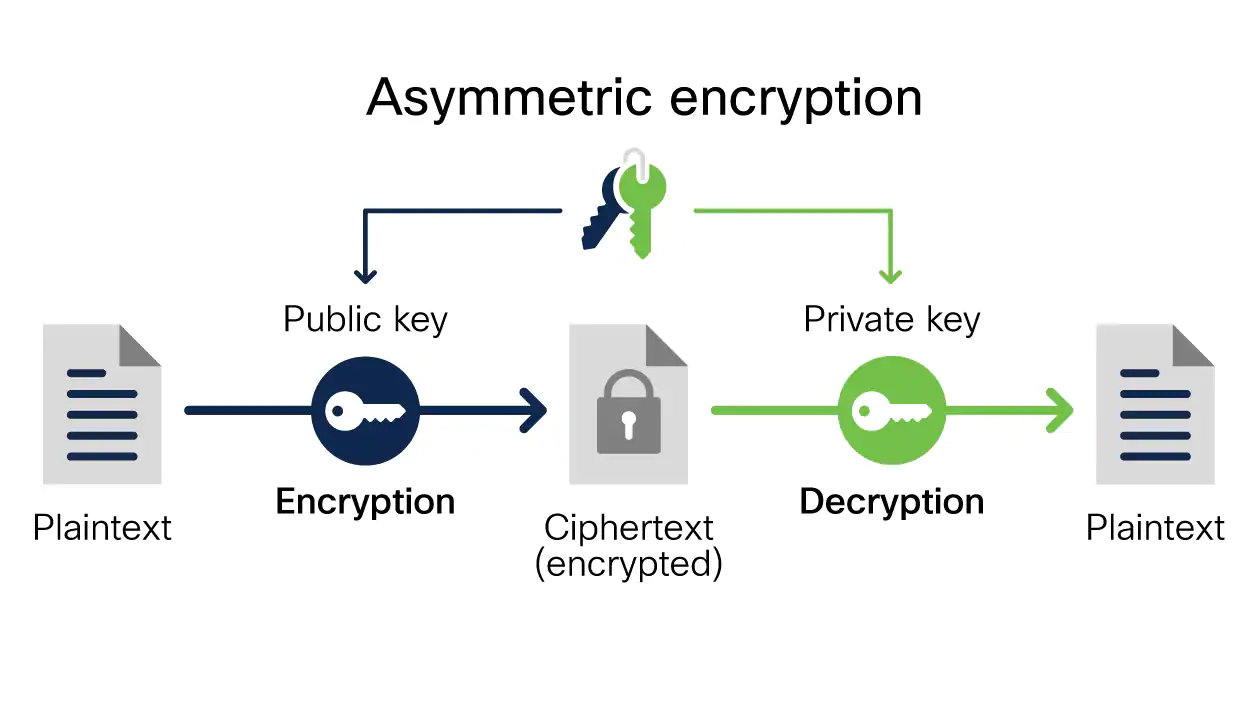
Public/private key pairs are often used to generate asymmetric ciphers. A single pair contains a public key and a corresponding private key. Anyone can encrypt a message with the public key; only the private key owner can decrypt it.
To send an encrypted email, you’ll need to install an application called PGP (Pretty Good Privacy). Once installed, you simply select a file to encrypt and choose whether you want to protect the entire file or just specific parts. You can add attachments too.
Enter your recipient’s address and press Send when ready to send the message. If everything goes according to plan, the recipient receives an encrypted version of the message, complete with a digital signature showing that it came from you and wasn’t altered along the way.
What is a key in cryptography?
A cryptographic key is a string or sequence of characters used within an encrypted file or system to alter the information. Unlike a password, which must be memorized, a key can be generated automatically without human input.
Cryptographic keys are usually stored in a secure location such as a safe deposit box or vault. They are often protected by a combination lock or a PIN code.
When needed, they are entered into a cipher machine or cryptograph device. This process allows the data to be decrypted (unlocked), revealing the original text.
The term “key” often refers to a symmetric key. Symmetric keys are commonly used in public key infrastructure (PKI). In PKI, a pair of keys—a public key and a private key—are used to encrypt and decrypt messages.
An asymmetric key is used to generate a symmetric key. For example, RSA uses a public/private key pair to encrypt communications. The public key encrypts data, while the private key decrypts the data.
Types of Encryption
Symmetric Encryption
Both parties use the same secret key to cipher and decipher the data in this simple encryption method. This type of encryption is called symmetric because both parties are required to know the key before they can begin communicating.
If someone intercepts the communication, they won’t be able to read it without knowing the key. However, if the key is compromised, anyone can access the data.
The most common form of symmetric encryption is known as the Advanced Encryption Standard (AES). There are three types of AES: 128-, 192-, and 256-bit keys.
Each version uses a different number of rounds to perform cryptographic operations. For example, AES-256 uses eight rounds, while AES-128 uses four.
While symmetric encryption is considered secure, it does require a lot of computing power. To make things worse, it takes longer to transmit data over the internet than asymmetric encryption methods.
Asymmetric encryption involves two separate keys—one public and one private. One party encrypts the data with the public key, and the second party uses her private key to decrypt the data.
Asymmetric encryption is much easier to implement than symmetric encryption. Both parties don’t need to exchange the same secret key beforehand.
They simply generate their respective public/private key pairs and exchange the public keys via email or text messages. Once the public keys are exchanged, each person can start sending encrypted messages to the other.
Asymmetric Encryption
Also known as public key cryptography or PGP, asymmetric encryption is based on the premise that there are two types of keys: public and private. A public key is something anyone can use to send you messages, whereas a private key is something only you know how to unlock.
Public key cryptography is commonly used to secure online transactions such as email, web browsing, and file sharing.
When you receive a message, you verify the sender’s public key to ensure that he is indeed who he claims to be. If you find his public key to match what you already know about him, you accept the message without question.
Private keys are kept safe and secret. They encrypt sensitive files, passwords, and other personal information. You cannot access the contents of encrypted documents unless you possess the corresponding private key.
Both symmetric and asymmetric encryption methods are widely used today. Symmetric algorithms work well for bulk data, while asymmetric algorithms are better suited for small amounts of confidential data.
Data Encryption Standard (DES)
The Data Encryption Standard (DES), also known as Triple DES or 3DES, is a block cipher used in many cryptographic protocols. It was published in 1977 by NBS/NIST as Federal Information Processing Standards Publication 46, which specified three different modes of operation: Electronic Codebook (ECB), Cipher Block Chaining (CBC), and Output Feedback (OFB). In 1982 it became part of FIPS PUB 81.
DES is a symmetric key system that uses 56-bit keys. This makes DES vulnerable to brute force attacks because there are 2128 possible keys. On average, a 64-byte key can be cracked in about one second, while a 128-byte key takes approximately 5 minutes.
In 1998, the United States National Institute of Standards and Technology (NIST) recommended replacing DES with Advanced Encryption Standard (AES). However, some governments, such as China, still use DES.
Triple Data Encryption Standard (3DES)
The Triple Data Encryption Standard (TDE), also known as 3DES, was designed to replace the Data Encryption Standard (DES).
This standard involves running the DES algorithm three different times, each with a different key.
In contrast to DES, where one key is used for encrypting data, multiple keys are needed for 3DES. The Triple Data Encryption Algorithm (TDES) was standardized in 1995 and adopted in 1997.
RSA
The RSA algorithm is named after three mathematicians: Ron Rivest, Adi Shamir, and Leonard Adleman. Their contribution was published in 1977 and became widely known as the RSA algorithm. It is based on a mathematical problem called factoring large numbers into prime factors.
In cryptography, RSA stands for “Rivest–Shamir–Adleman.” This name refers to the three authors who developed the algorithm.
Advanced Encryption Standard (AES)
The Advanced Encryption Standard (Aes), developed by the National Institute of Standards and Technology (Nist) in 1997, is a symmetric encryption algorithm.
Like many ciphers, it only uses a secret key known to the sender and receiver. Aes provides three different key sizes—128 bits, 192 bits, and 256 bits.
The standard specifies several modes of operation, including Electronic Code Book (ECB), Cipher Block Chaining (CBC), Output Feedback Mode (OFBM), and Counter mode (CTR). These are often referred to as “block ciphers” since each block of plaintext is encrypted separately.
In addition to being used for bulk data protection, AES is commonly employed in protocols requiring confidentiality, integrity, and authentication. For example, the Internet Key Exchange protocol (IKE) uses AES to provide confidentiality, integrity, and authentication for secure communications.
Encryption in the Cloud
Cloud encryption is a feature offered by cloud storage providers which encrypt the initial contents of files uploaded to the cloud.
Typically, three types of encryption are used in cloud environments: symmetric encryption, asymmetric public/private key cryptography, and hashing.
Symmetric encryption uses a unique key to both encrypt and decrypt information. Asymmetric public/private key pairs use two keys: one for encryption (public) and another for decryption (private).
Hashing algorithms take input data and produce output based on a mathematical function.
The primary advantage of cloud encryption is that it allows companies to store their sensitive data in the cloud without worrying about how secure it is.
However, cloud encryption also introduces several challenges. For example, cloud encryption typically provides access control mechanisms that allow authorized individuals to view and manipulate data while preventing unauthorized parties from accessing data.
These access controls require additional resources and attention to detail. In addition, cloud encryption can consume significant amounts of network bandwidth.
If you’re storing large volumes of data in the cloud, you’ll want to ensure enough bandwidth to support the amount of traffic needed to transfer the data securely.
Finally, encryption algorithms are designed to protect against certain kinds of attacks, so they don’t always provide adequate protection against others.
Many vendors now offer cloud encryption solutions. Some providers focus on particular aspects of encryption, including identity and access management, policy enforcement, and encryption key management.
Others provide full EaaS solutions that include both encryption and key management capabilities. And still, others focus on providing just encryption services.
Whether you implement cloud encryption yourself or outsource it to a vendor, it’s important to understand what type of solution you need and how it works.
You’ll also need to know what level of encryption you need and how much bandwidth it will consume. Once you have those things figured out, you can begin planning your implementation strategy.
End-to-End Encryption
End-to-end encryption refers to communication protocols ensuring that only the two people communicating can see what is being sent over the network.
This makes it impossible for anyone else to intercept the data, including the intermediary, like a telecom or internet service provider.
End-to-end encrypted communications include apps such as Signal and Telegram, which claim to offer the highest levels of security possible.
These apps encrypt the entire conversation, meaning no third party can access the contents of the messages.
They allow for some metadata to remain visible, such as the date and time of the chat. Still, this information can easily be removed without compromising the integrity of the conversation.
In addition to providing privacy for users, end-to-end cryptography offers several benefits to businesses and governments.
For example, companies can use it to protect sensitive customer data and prevent employees from leaking confidential information.
Governments can use it to keep secret intelligence operations hidden from prying eyes.
And law enforcement agencies can use it to investigate crimes without tipping off criminals about their investigation.
Why is data encryption necessary?
Data security is important because it protects against many threats, including malware, phishing scams, ransomware, and man-in-the-middle attacks. For example, consider a scenario where you are shopping online.
You enter payment information into a site, and the site sends the information to your bank.
However, the attacker has modified the code on the server side to capture the credit card number and send it to a different location.
In this case, the attacker could charge purchases to your account even though you never entered the credit card number into the site.
Encryption ensures that data in transit is protected during transmission over the network. If the connection is intercepted, the data cannot be read by anyone else.
Similarly, encryption enables communication partners to exchange sensitive data securely. An email sent via SSL/TLS provides confidentiality, authentication, and integrity protection, while an unencrypted email does not provide any of those protections.
Finally, data integrity means ensuring that the data received matches the original data sent. A compromised computer system could alter the data being exchanged.
What is an encryption algorithm?
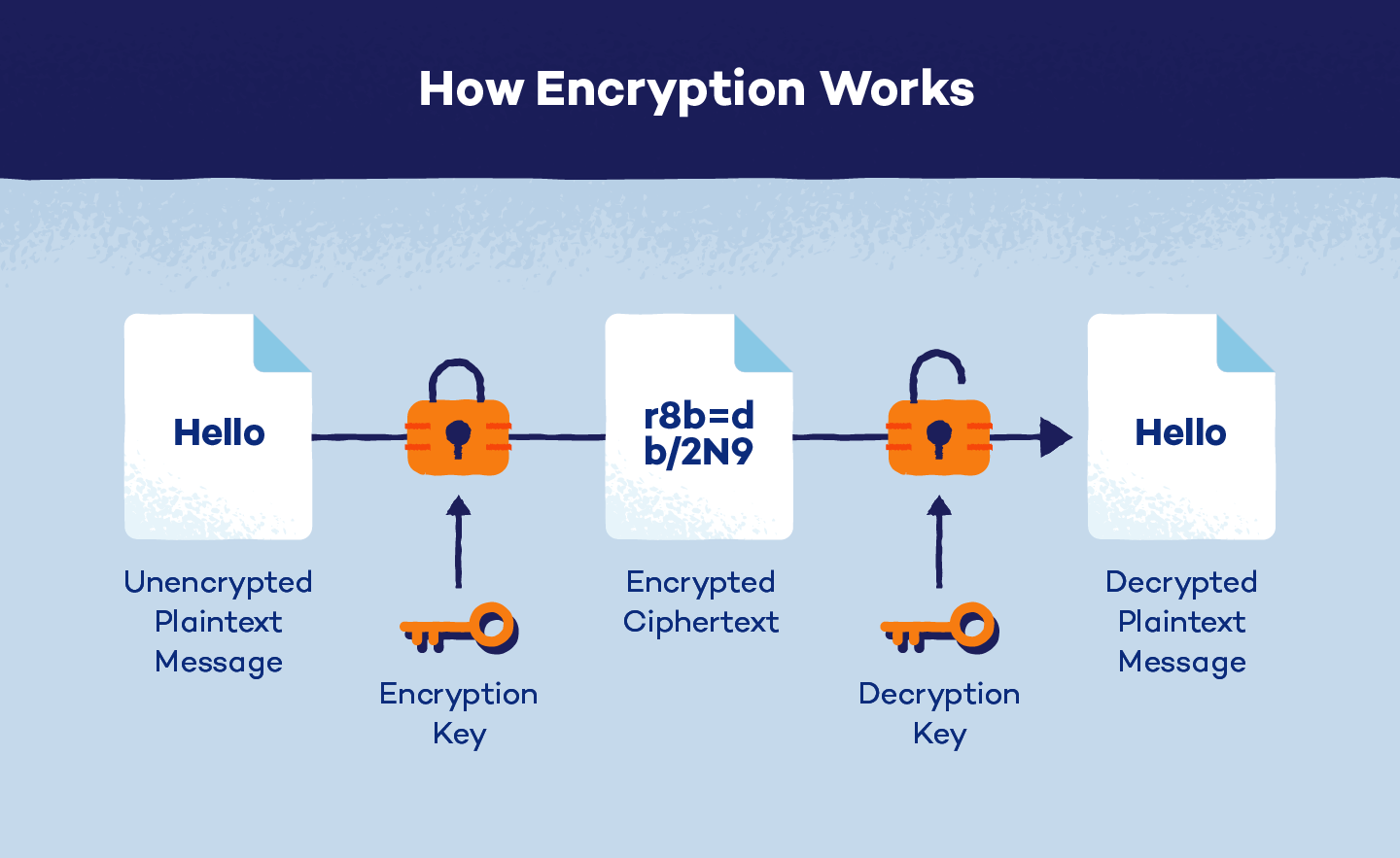
An encryption algorithm is a method you use to encrypt something. You take some information, like a text file, and turn it into ciphertext — a string of letters or numbers that looks completely different.
This is done by applying an algorithm, which takes the original piece of information and turns it into another string of letters or numbers. The original information appears again when the encrypted data is decrypted using the same key.
The most common type of encryption is symmetric cryptography because both parties must know the same secret key to decrypt the data. Symmetric algorithms are usually slower than asymmetric ones but offer better security.
Asymmetric algorithms work differently. One party knows the secret key; the other does not. Asymmetric algorithms are much faster than symmetric algorithms, making them ideal for online banking transactions.
They also provide greater privacy because no one needs to know the key to read someone else’s messages.
How Does Encryption Work?
Encryption works just like locks do. When you lock your door, you use a key to open it. This key is something you know—it’s usually written down somewhere and kept safe. If someone else wants to unlock your door, they need a matching key. A good lock won’t let anyone open it without the correct key.
The same thing happens with encryption. An encryption key ensures that people who don’t have access to the information cannot read it.
You might think of it like how you keep track of who gets into your house. Only you know the code for the front door. Anyone else needs a copy of that code to get inside.
When you encrypt data, three things are involved: a cipher, a key, and some plain text. Cipher stands for “ciphertext.” Plain text is the actual information you want to send over the internet.
The ciphertext is the information that has been encoded into a secret form. In this case, the secret form is called a cipher.
The ciphertext is sent to the recipient. They use the same key to decipher it back into plain text. Deciphering is similar to unlocking a door. To decrypt the data, they need the same key you had when you originally encrypted it.
What is a brute force attack in encryption?
Bruteforce attacks are one of the most common ways hackers attempt to break into encrypted data. They use software designed to make thousands or even millions of guesses per second.
A brute force attack requires the hacker to find out what the password is without knowing it. This happens because many possible combinations of letters and numbers could be used to form a password.
If you had a list of every combination of five letters and four digits that could be used to create a password, there would be over 10^32 possibilities.
Even if you did not try each possibility, there are too many to test exhaustively. So, instead, we rely on algorithms that quickly narrow down the number of possibilities.
These algorithms work by testing different permutations of the letter and digit combinations to see if they match the target string.
For example, let’s say our target is abc123. We might start by trying aa1231, followed by aaa2311, etc. If none of those matches, we move on to bb1321, cc1231, etc., and so forth.
If none works, we move on to ccc3121, ddd3321, etc. Eventually, we will run out of options and stop looking. We can discover the correct combination by running through a large enough set of permutations.
How is encryption used to keep Internet browsing secure?
Encryption is foundational for many technologies, including email, instant messaging, voice calls, and online banking. But it is especially important for protecting web traffic because it prevents eavesdroppers from intercepting data.
The protocol responsible for this is known as Hypertext Transfer Protocol Secure (HTTPS), and it uses the encryption protocol known as Transport Layer Security (TTL).
This indicates that the site is encrypted and safe from snoopers.
SSLv3 was once the default encryption protocol for web browsers, but TLS has now replaced SSLv3.
If you implement HTTPS for your site, you’ll likely need to install a TLS certificate from your web host. These certificates are used to secure encrypted connections between browsers and websites.
Conclusion
Encryption is a process of transforming readable data into an unreadable format. This is done using various algorithms, making it difficult for unauthorized individuals to access the information.
There are three main types of encryption: symmetric, asymmetric, and hashing.
Symmetric encryption is the most common and uses the same key to encrypt and decrypt data. Asymmetric encryption uses two keys, one for encryption and one for decryption.